Hallo, ich bin Sarah.
Geboren 1981 in Kandersteg. Akute Bergflucht in den Jugendjahren. Handelsschülerin in La Neuveville. Weltenbummlerin und Gelegenheitsjobberin. Studentin an der Fachhochschule für Wirtschaft und Kommunikation in Luzern. Redaktorin bei der Gratiszeitung «.ch», der Nachrichtenagentur SDA, der SDA/AWP Multimedia und beim SRF. Pferdepflegerin in England. Mädchen für alles in Backpacker in Cadiz. Hüttengehilfin in der Doldenhornhütte. Vor zehn Jahren den Weg in die Selbstständigkeit gesucht und gefunden. Bernerin. Mutter.
Was ich mache
Journalistin. Schreiben, recherchieren, lieber vor Ort als am Laptop und natürlich zuhören und (hinter)fragen: Dafür schlägt mein Herz. Getrieben von einer Neugierde auf (fast) alles und jeden, begeistern mich Menschen, Gesellschaften und Beziehungen – manchmal betrüben oder befremden sie mich auch. Daraus entstehen Geschichten, Porträts und Interviews. Print oder Online und immer termingerecht.
PR-Texterin. Täglich übe ich den Spagat und stretche meine Beine hin zu süffisanten PR-Texten. Ich verfasse Newsletter für Verbände, liefere Beiträge für Kundenjournale und füttere soziale Medien mit lustigen Häppchen. Daneben stemme ich auch grössere Projekte: Von der Themensetzung bis zum "Gut zum Druck" begleite ich Magazine. Schreibe selbst und redigiere Texte von freien Schreiberinnen.
Ghostwriterin. Eitelkeit? Nicht so mein Ding. Mein Name? Schon wichtig und richtig aber nicht immer, überall und ständig. Wer also eine Rede schreiben muss, Unterstützung bei einem Buchprojekt braucht oder sonst auf eine Hilfskraft im Hintergrund angewiesen ist: Ich schreibe auch mit Herzblut und Hirnzellen für fremde Federn.
Ideenlieferantin. Meine Hirnzellen spinnen gerne und oft. Man kann sie deshalb auch mieten - sei es zum Brainstormen, zum Geschichten generieren oder Konzepte erarbeiten. Diese können durchaus auch grösser sein. Ich pflege ein kleines, feines Netzwerk mit Journalistinnen, Fotografen, Grafikerinnen, mit denen ich bei Bedarf zusammen arbeite.
Wer auf mich setzt
20 Minuten // Aargauer Zeitung // Alpine Rettung Schweiz // Annabelle // Berufsschullehrerverband // Coopzeitung // Die Alpen (SAC) // Globetrotter // Flirt don't hurt // Fritz und Fränzi // Geo // Handelszeitung // Hello Zurich // Hotel Revue // Kavallo // Miss Moneypenny // Postfinance // Reportagen// Restaurant Darling // SDA/AWP Multimedia // Surprise // SWISSAID // Tamedia // Workzeitung
Wie ich schreibe
Meine Lehre - Promis erzählen
Der Landwirt wurde Bundesrat, der Forstwart Schwingerkönig, und aus drei KV-Lernenden wurden die schnellste Rollstuhl-Sportlerin, Musikstar und Ständerätin. Für FOLIO blicken sie auf zurück.
Mithilfe Konzeption, Recherche, Kontaktanfragen und Interviews für das BCH Folio

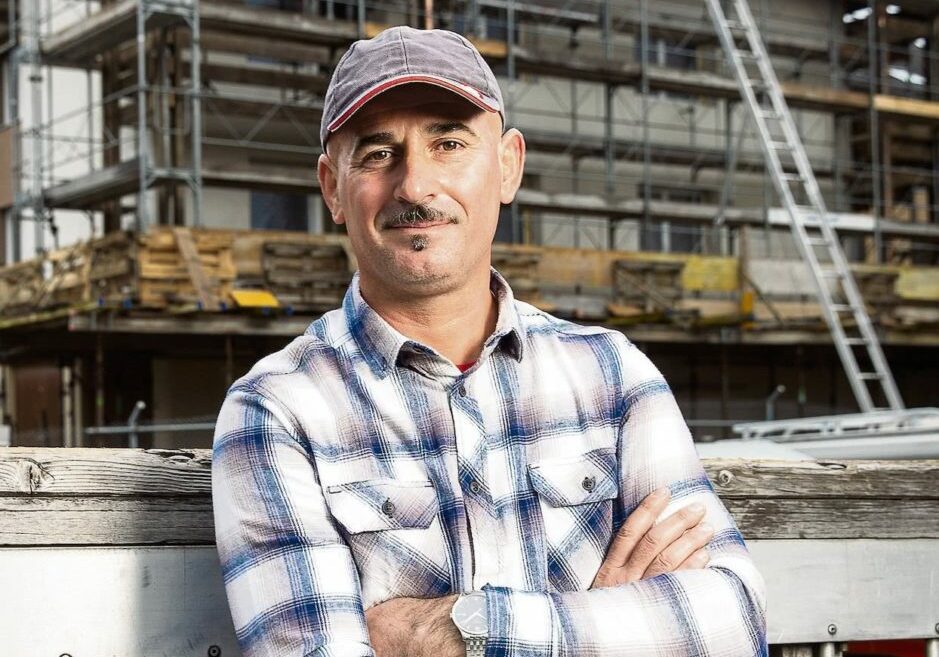
Die reich(haltig)e Unbekannte
Lange Zeit kannten man die Süsskartoffel in der Schweiz nicht. Das ändert sich: Die exotische Knolle ist auf dem Vormarsch. Auch dank innovativen Bauern wie Christian Hurni und Simon van der Veer.
Produzentenbericht für die Coopzeitung.
Foto: Ivan Steiner

Eiger, Mönch und Chinesen
Rettung auf Mandarin: Im Berner Oberland hofft man auf neue Skitouristen. Und zwar aus China. Die ersten Betriebe haben sich bereits auf die neuen Gäste eingestellt.
Reportage aus Mürren für das GEO Schweiz
Foto: Peter Klaunzer
Mail mir!
Sarah Forrer
Büro Bücherei
3013 Bern